COVID-19_arXiv on Twitter: "𝗧𝗶𝘁𝗹𝗲: Protocol for a Sequential, Prospective Meta-Analysis to Describe COVID-19 in Pregnancy and Newborn Periods. 𝗔𝘂𝘁𝗵𝗼𝗿𝘀: Emily R. Smith, Siran He, Erin M Oakley, Lior Miller, James M Tielsch

Mutating m909 Monoclonal Antibody to Target Folate Receptor Beta – IU Undergraduate Research Summer 2021 Poster Symposium

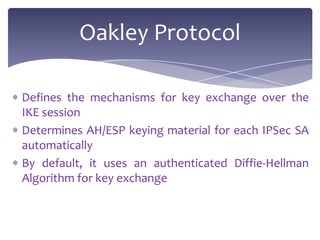
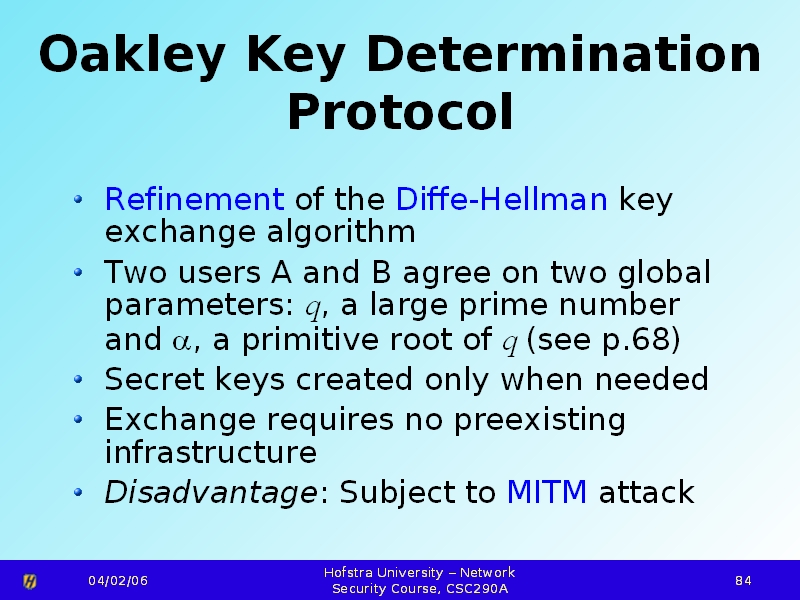
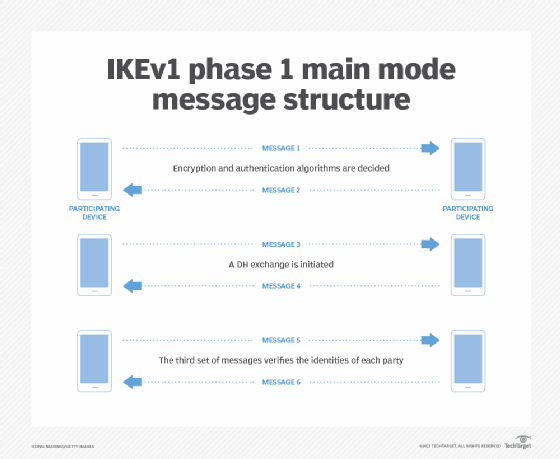
Internet Key Exchange: Security association, Oakley protocol, Diffie–Hellman key exchange, Internet Security Association and Key Management Protocol : Miller, Frederic P., Vandome, Agnes F., McBrewster, John: Libri - Amazon.it

Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice | January 2019 | Communications of the ACM

Computer Security and PGP: What Is Diffie - Hellman Key Exchange Protocol or Oakley Protocol? | Computer security, Security, Secret

Tom Cruise wears Oakley Sunglasses in Mission Impossible 4: Ghost Protocol | SelectSpecs Glasses Blog | Oakley, Oakley sunglasses, Sunglasses

Oakley Wind Jacket - Tom Cruise - Mission: Impossible – Ghost Protocol | Sunglasses ID - celebrity sunglasses

Oakley, Inc. Eyeglass prescription Sunglasses Oakley EVZero Path, Hypertext Transfer Protocol, lens, fashion, glasses png | PNGWing





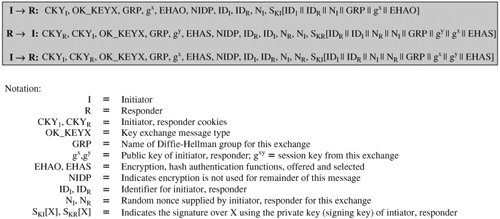

![Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram](https://www.researchgate.net/profile/Riaz-Khan-19/publication/297336095/figure/fig4/AS:558684922224640@1510212273285/Operation-of-SA-other-protocols-OAKLEY-SKEME-and-ISAKMP-8-5-OAKLEY-it-is-a-key.png)
![Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram Operation of SA other protocols: OAKLEY, SKEME and ISAKMP [8] [5].... | Download Scientific Diagram](https://www.researchgate.net/profile/Riaz-Khan-19/publication/297336095/figure/fig4/AS:558684922224640@1510212273285/Operation-of-SA-other-protocols-OAKLEY-SKEME-and-ISAKMP-8-5-OAKLEY-it-is-a-key_Q320.jpg)